

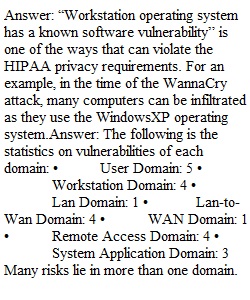
Q 1. Health care organizations must strictly comply with the Health Insurance Portability and Accountability Act (HIPAA) Privacy and Security rules that require organizations to have proper security controls for handling personal information referred to as “protected health information,” or PHI. This includes security controls for the IT infrastructure handling PHI. Which of the listed risks, threats, or vulnerabilities can violate HIPAA privacy and security requirements? List one and justify your answer in one or two sentences.2. How many threats and vulnerabilities did you find that impacted risk in each of the seven domains of a typical IT infrastructure?3. Which domain(s) had the greatest number of risks, threats, and vulnerabilities?4. What is the risk impact or risk factor (critical, major, and minor) that you would qualitatively assign to the risks, threats, and vulnerabilities you identified for the LAN-to-WAN Domain for the health care and HIPAA compliance scenario?5. Of the three System/Application Domain risks, threats, and vulnerabilities identified, which one requires a disaster recovery plan and business continuity plan to maintain continued operations during a catastrophic outage?
View Related Questions